Automate setting ‘Retain indefinitely’ flag on your releases
Overview
As a common practice, after a successful release to production, often there is a need to retain the involved artifact and relevant release information for a certain amount of time. In order to avoid that a retention policy removes this information, you will mark that release with a Retain indefinitely flag, by choosing that option from the VSTS UI.
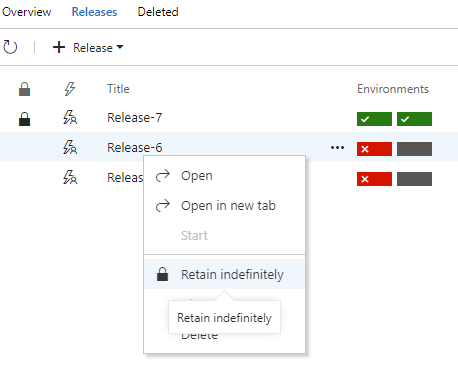
As this is a manual process that I would like to automate, I will use the Retain indefinitely current release task available in VSTS Marketplace.
After installing the extension, in the list of available tasks, check the Utility category and you’ll find the above-mentioned task.
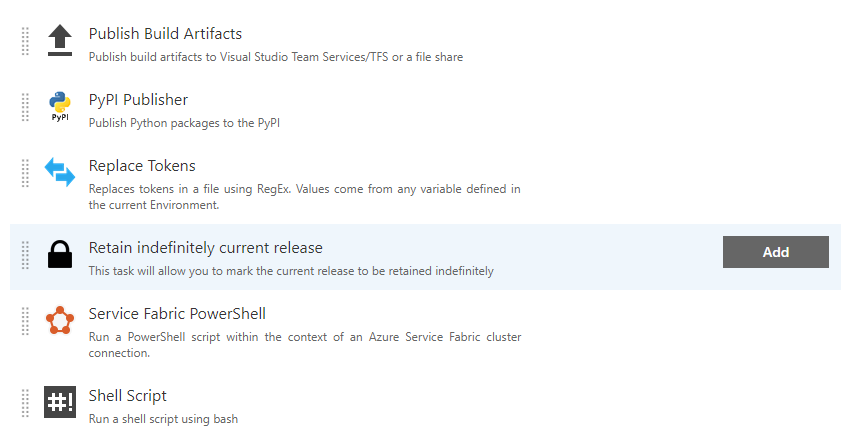
Only a single parameter is presented by the task in a form of a checkbox labelled Mark the current release to be retained indefinitely. By default is set to true. If checked, it will mark the current release with Retain indefinitely flag. Otherwise, it will take the Retain indefinitely flag off the current release.
I will add it only to my production environment process and I will place it as the last task. E.g.
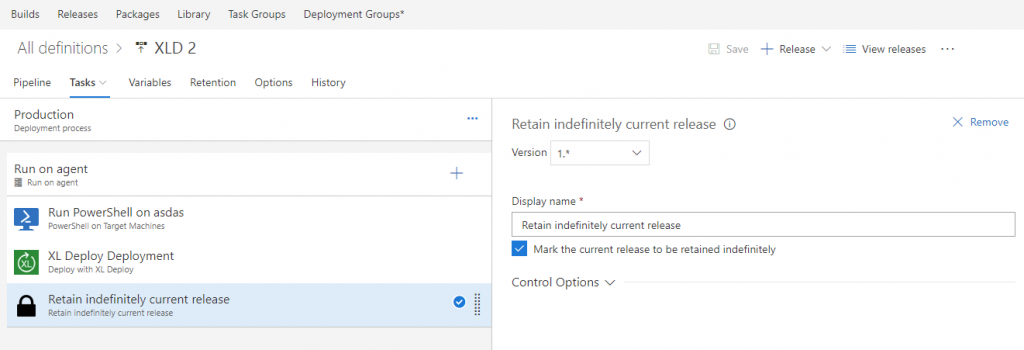
This is because I do not want this task to execute if any of the previous tasks in the process do fail. It should execute only if I managed to deploy my application in production. That is the criteria for retaining this release for a longer time.
The only requirement for this task to run is that the account on which the build agent is running has sufficient privileges to set Retain indefinitely flag.
That’s all. Now you do not need to remember to set the Retain indefinitely flag after every successful production release.
UPDATE:
After extensive testing, I noticed that it’s mostly the case that additional rights do need to be granted for the build agent identity in order for this task to succeed.
In case the permissions are missing, a similar error will be visible in the log:
##[error]VS402904: Access denied: User Project Collection Build Service (mummy) does not have manage releases permission. Contact your release manager.
Edit the security settings for that particular release or for all the releases and set the following to the needed account.
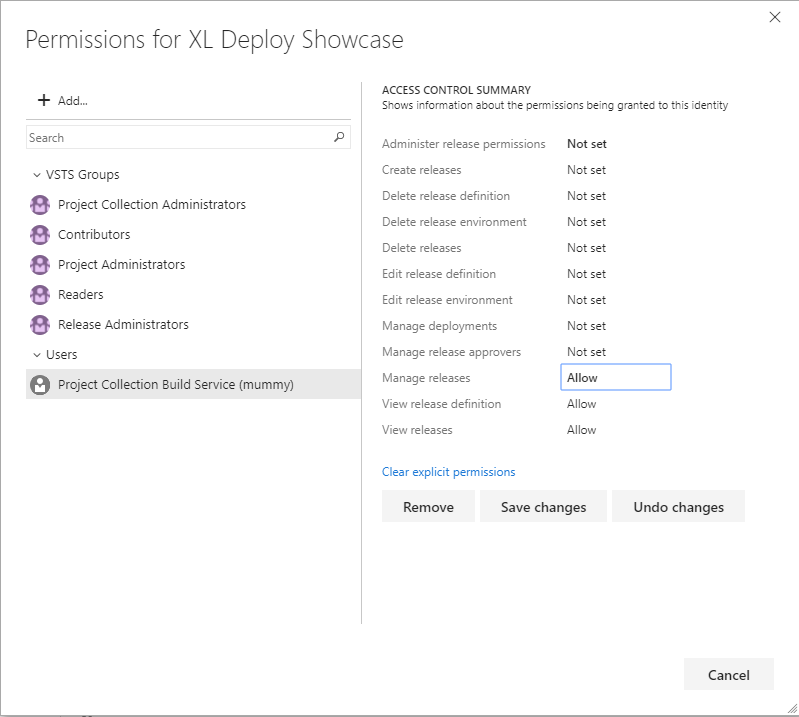
Make sure ‘Manage Releases’ permission is granted for the indicated user.
Another note is that also the cross-platform agents are supported starting from the version 2.x of the extension. If you check on GitHub you’ll see that the task has been re-written and it is now based on node provider with the code written in TypeScript.